نتایج جستجو

Application Security in the ISO27001 Environment
Vinod Vasudevan, Anoop Mangla, Firosh Ummer, Sachin Shetty, Sangita Pakala, 2008
E mail Security A Pocket Guide
Paul Dowland, 2010
E-Mail Security: A Pocket Guide
It Governance Publishing, 2010
Managing Information Security Breaches
Michael Krausz, 2010
Virtualization security: protecting virtualized environments
Dave Shackleford, 2012
Counter-Terrorism Policing: Community, Cohesion and Security
Sharon Pickering, 2008
Fluid Security in the Asia Pacific: Transnational Lives, Human Rights and State Control
Claudia Tazreiter, 2016
Security Assessment in Vehicular Networks
Suguo Du, 2013
Vehicular Ad Hoc Network Security and Privacy
Xiaodong Lin, 2015
Security Warrior
Cyrus Peikari, 2004
Security warrior
Cyrus Peikari, 2004
Security Warrior
Cyrus Peikari, 2004
802.11 Security
Bruce Potter, 2002
Toward the National Security State: Civil-Military Relations during World War II
Brian Waddell, 2008
Cyber Power: Crime, Conflict and Security in Cyberspace
Solange Ghernaouti-Helie, 2013
New Biotechnologies for Increased Energy Security : The Future of Fuel
Serrano-Ruiz, 2015
Environmental Change and Security: A European Perspective
Walter Hirche (auth.), 1999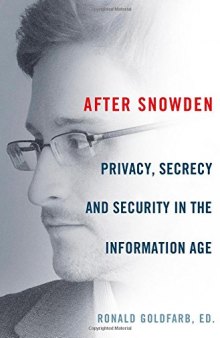
After Snowden: Privacy, Secrecy, and Security in the Information Age
Ronald Goldfarb, 2015