نتایج جستجو

Information Security and Cryptology – ICISC 2012: 15th International Conference, Seoul, Korea, November 28-30, 2012, Revised Selected Papers
Thore Graepel, Kristin Lauter, Michael Naehrig (auth.), Taekyoung Kwon, Mun-Kyu Lee, Daesung Kwon (eds.), 2013
Nanobiosensors and Nanobioanalyses
Mun'delanji C. Vestergaard, Kagan Kerman, I-Ming Hsing, Eiichi Tamiya (eds.), 2015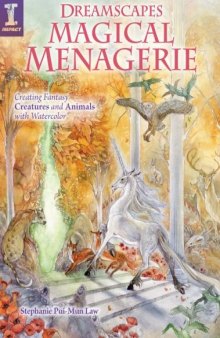
Dreamscapes Magical Menagerie: Creating Fantasy Creatures and Animals with Watercolor
Stephanie Pui-Mun Law, 2012
Al-Ma’mun
Michael Cooperson, 2005
Early Study-Abroad and Identities: Korean Early Study-Abroad Undergraduates
Mun Woo Lee (auth.), 2016
Modeling Risk
Johnathan Mun, 2010
Modeling risk
Johnathan Mun, 2006
Real options analysis
Johnathan Mun, 2002
Real Options Analysis Course - Business Cases and Software Applications
Johnathan Mun, 2003
Real Options Analysis Course : Business Cases and Software Applications
Johnathan Mun, 2003
Real Options Analysis Course: Business Cases and Software Applications
Johnathan Mun, 2003
Dreamscapes: Creating Magical Angel, Faery & Mermaid Worlds In Watercolor
Stephanie Pui-Mun Law, 2008
Understanding IPv6
Youngsong Mun, 2005
Dreamscapes Fantasy Worlds Create Engaging Scenes and Landscapes in Watercolor
Stephanie Pui-Mun Law, 2014
Understanding IPv6
Youngsong Mun, 2005
Spiritual Biography photos
Ven. Acariya Mun









